Starting with Orka 3.0, Orka uses Single Sign-On (SSO) and Kubernetes role-based access control (RBAC) for user management. Users log in with their MacStadium Customer Portal credentials. What they can do depends on the role assigned to their account.Documentation Index
Fetch the complete documentation index at: https://docs.macstadium.com/llms.txt
Use this file to discover all available pages before exploring further.
How roles work
Roles exist in two places: the Customer Portal and the Orka cluster. They map to each other based on the role assigned in the Portal. Customer Portal roles:- Admin: full control of the Portal account and the Orka cluster. Can invite users, manage billing, and administer cluster resources.
- Tech: developer access. Can deploy and manage VMs, images, and VM configs. Cannot manage users or namespaces.
- Billing: read-only Portal access. Cannot perform any cluster actions.
- Admin Portal users get the Administrator cluster role.
- Tech Portal users get the Technical cluster role.
- Service accounts are cluster-only accounts for CI/CD integrations. They are not tied to a Portal account.
Role-based access matrix
Within the Customer Portal, the Admin, Tech, and Billing roles have the following capabilities: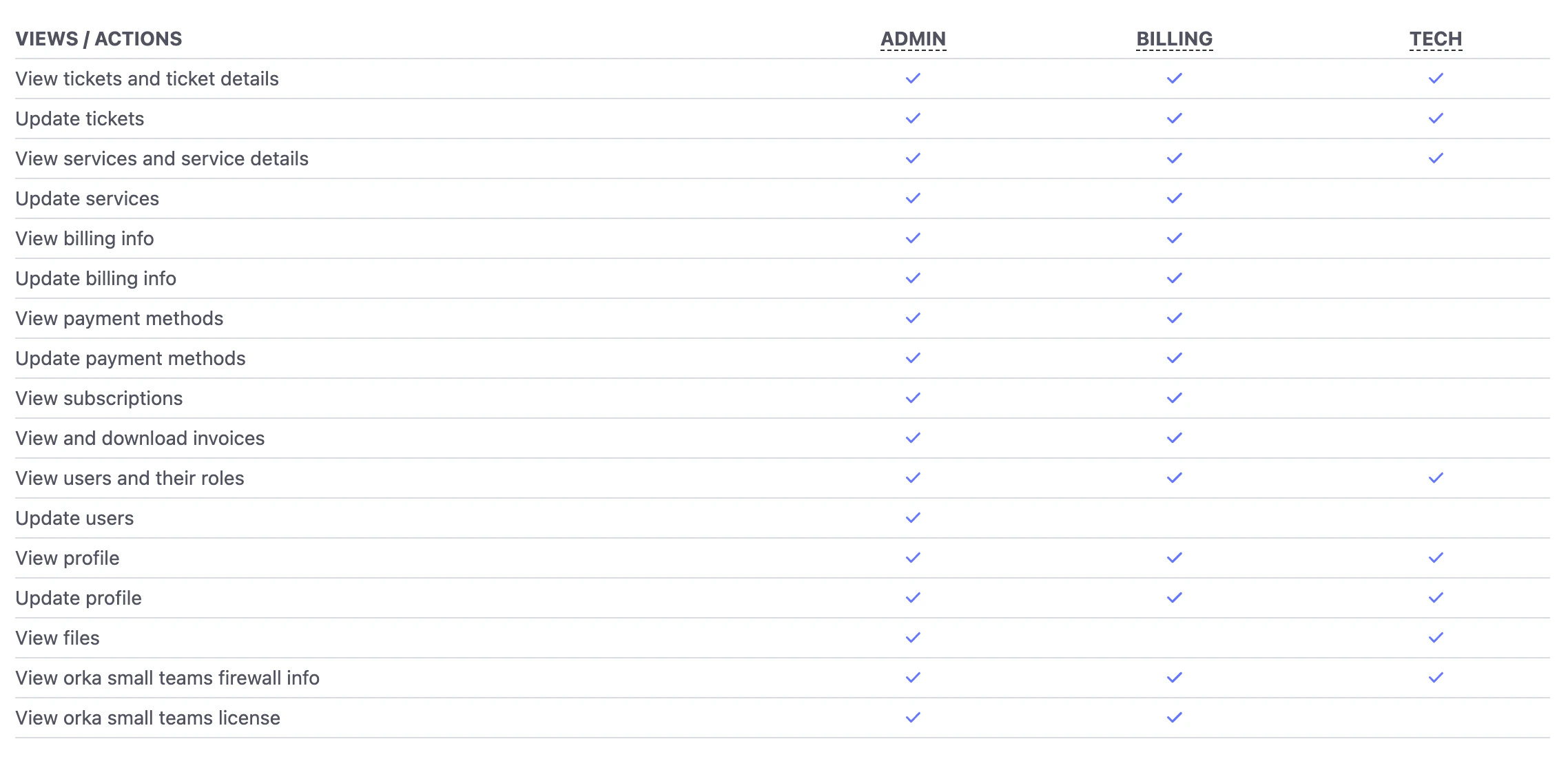
| Operation | Admin | Tech | Billing | Admin SA (Orka Small Teams-only) | Regular SA |
|---|---|---|---|---|---|
| Log in with CP credentials | ✅ | ✅ | ✅ | ❌ | ❌ |
| Log in with authentication token | ✅ | ✅ | ❌ | ✅ | ✅ |
| Log out | ✅ | ✅ | ✅ | ✅ | ✅ |
| Manage users | ✅ | ❌ | ❌ | ❌ | ❌ |
| Manage service accounts, including token generation | ✅ | ❌ | ❌ | ✅ | ❌ |
| Print authentication token | ✅ | ✅ | ✅ | ✅ | ✅ |
| Manage namespaces | ✅ | ❌ | ❌ | ✅ | ❌ |
| Manage role bindings | ✅ | ❌ | ❌ | ✅ | ❌ |
| List nodes | ✅ | ✅ | ❌ | ✅ | ✅ |
| Manage nodes | ✅ | ❌ | ❌ | ✅ | ❌ |
Access and work in the orka-default namespace | ✅ | Yes (Admin can revoke access) | ❌ | ✅ | If created in orka-default; otherwise based on role bindings |
Access and work in custom orka- namespaces | ✅ | Based on role bindings | ❌ | ✅ | If created in the namespace; otherwise based on role bindings |
| View information about all VMs in the namespace | ✅ | ✅ | ❌ | ✅ | ✅ |
| Deploy VMs in the namespace | ✅ | ✅ | ❌ | ✅ | ✅ |
| Manage the VM state of all VMs in the namespace | ✅ | ✅ | ❌ | ✅ | ✅ |
| Delete own VMs in the namespace | ✅ | ✅ | ❌ | ✅ | ✅ |
| Delete other subjects’ VMs in the namespace | ✅ | ❌ | ❌ | ✅ | ❌ |
| Manage VM configs (except deleting) | ✅ | ✅ | ❌ | ✅ | ✅ |
| Delete own VM configs | ✅ | ✅ | ❌ | ✅ | ✅ |
| Delete other owners’ VMs | ✅ | ❌ | ❌ | ✅ | ❌ |
| Manage images | ✅ | ✅ | ❌ | ✅ | ✅ |
| List and pull remote images | ✅ | ✅ | ❌ | ✅ | ✅ |
| Manage ISOs | ✅ | ✅ | ❌ | ✅ | ✅ |
| List and pull remote ISOs | ✅ | ✅ | ❌ | ✅ | ✅ |
Common admin workflows
These are the most frequent access management tasks an Orka cluster administrator performs.Adding a user to the cluster
- In the MacStadium Customer Portal, an account Admin invites the user and sets their role (Admin or Tech).
- The user accepts the invite and sets their credentials.
- The user logs in to the Orka cluster with their Portal credentials.
Adding a service account for CI/CD
- A cluster administrator creates the service account in the target namespace.
- If the service account needs access to additional namespaces, the administrator configures the appropriate role bindings.
Isolating resources with namespaces
Administrators can create namespaces to dedicate resources to specific teams or workflows.- Create the namespace.
- Assign nodes to the namespace. (Nodes cannot be shared across namespaces.)
- Add users or service accounts as subjects to the namespace’s role binding.
Modifying or revoking access
- To change a user’s role or disable them: edit or disable their account in the MacStadium Customer Portal.
- To revoke a service account’s access: delete the service account in the Orka cluster.
- To add or remove namespace access: update the relevant role bindings in the cluster.
Key terms
| Term | Where | Definition |
|---|---|---|
| Account | Customer Portal | The top-level entity managing one or more Orka clusters. All account users are shared across clusters on the same account. |
| Account user | Customer Portal | A person belonging to the account. Can assume one role: Admin, Tech, or Billing. |
| Cluster user | Orka cluster | A Portal account user who has logged in to the cluster. Maps to Administrator or Technical based on their Portal role. |
| Service account | Orka cluster | A cluster-only account for CI/CD integrations. Not linked to a Portal account; tokens are valid for 1 year by default. |
| Namespace | Orka cluster | Isolates resources (VMs, images, nodes) from other namespaces. Users and service accounts need explicit role binding access to each namespace. |
| Role | Orka cluster | A Kubernetes RBAC role: Administrator or Technical. Created automatically when a namespace is created. |
| Role binding | Orka cluster | Links cluster users or service accounts to a namespace. Admins manage role binding subjects manually. |

